Claims covered under a Cyber policy are very broad, but are typically three core things: Liability (privacy lawsuits and regulatory defence), Internal Financial Loss (extortion, notification expenses, data recovery, business interruption, crime/theft), and Emergency Incident Response (costs incurred from responding to a Cyber Event).

| Cyber Insurance provides cover for financial loss and expenses that businesses may suffer as a result of a Cyber Event, including cyber attacks from malware or other invasive software, cyber extortion and social engineering. | Claims covered under a Cyber policy are very broad, but are typically three core things: Liability (privacy lawsuits and regulatory defence), Internal Financial Loss (extortion, notification expenses, data recovery, business interruption, crime/theft), and Emergency Incident Response (costs incurred from responding to a Cyber Event). |
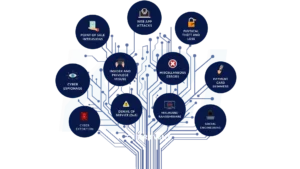
A Cyber Event triggers a claim on a Cyber Insurance policy and can be caused by several different scenarios:
What are the Coverages Available?
Main Coverages that respond to a Cyber Event:
1. Privacy Breach Notification & Crisis Management Costs
| When a cyber incident occurs, whether it is through some kind of invasive software (malware, ransomware), phishing or social engineering scheme, or other form of cyber attack, there is usually a privacy breach as a result – i.e. private or confidential information/data is exposed. This policy section provides cover for the costs associated with responding to a privacy breach, including: |
|
2. Privacy & Security Liability
| This section protects you from claims/lawsuits as a result of a privacy and security wrongful act, such as:
|
|
3. Cyber Extortion
| Cyber extortion is defined as a threat against the insured computer system to provide ransom in order to prevent a Cyber Attack. | Coverage for this can include: the payment of a ransom, negotiation & mediation costs, crisis management costs & costs to resolve a security threat, and investigation costs to determine the cause of the extortion threat. |
4. Business Interruption – Loss of Profits & Operational Expenses
| Coverage for loss of profits and additional operating expenses incurred because of a cyber event. |
5. Data Recovery & System Damage
| This section covers the costs and expenses for lost, damaged or destroyed IT systems, records, and data. | This can include the retrieving, repairing, restoring or replacing of data or systems, including the removal of malware. |
6. Regulatory Defence and Fines
| This section provides cover for defence costs and regulatory fines that have resulted from a cyber incident, such as a privacy or security breach. |
7. Media Liability
| Coverage for the following incidents that occur from your information through traditional and digital media:
|
|
Additional Coverage Sections and Policy Options:
1. Social Engineering & Funds Transfer
| The fraudulent transfer or theft of funds caused by instructions made by a person purporting to be an authorized employee, outsourced provider or customer of yours. | This coverage is typically sub-limited. |
2. Contingent Business Interruption
| Coverage for loss of profits and additional operating expenses incurred as a result of an interruption to a dependant business/supply chain partner, caused by a cyber event. |
3. Payment Card Data Security Liability
| Coverage for loss of profits and additional operating expenses incurred as a result of an interruption to a dependant business/supply chain partner, caused by a cyber event. |

What is a Cyber Attack or Data Breach?
| A cyber attack is usually associated with some sort of event that causes a loss, such as the outbreak of malware or other invasive software, cyber extortion or ransomware, and social engineering. A cyber event can also cause a data breach, which is defined as when personal information an organisation holds is lost or subjected to unauthorised access or disclosure. | Companies are encouraged to do everything in their power to prevent a cyber attack from ever occurring, but these are inevitably going to happen to most companies at some point – 1 in 4 companies experience a cyber attack at least once according to recent statistics. This is why it is necessary to have some kind of cyber incident response plan; or at least an idea of what to do if you experience a cyber attack or data breach. |

7 Step Plan on What to Do Following a Cyber Event

1. Identify The Breach
| This may seem like an obvious step, but cyber breaches often occur without the victim even noticing – sometimes sitting in your system or on your computer for months before an actual attack occurs. Identifying the breach can be as simple as training staff to recognise a breach when it happens, to implementing sophisticated breach prevention software. | No matter how this is done, it is important to identify a breach quickly, so you can respond to it right away. Once you’ve realised that a breach has occurred, you’ll need to identify what has happened and proceed to the next step – at this point you can contact your incident response team. |
2. Contact Incident Response Hotline
| Who do you call in the event of a cyber attack? | One of the main reasons we recommend purchasing a Cyber Insurance policy is because it gives you immediate access to a 24/7 emergency hotline, so you have somebody to call in the event of a breach. This puts you in touch with experts who can sort out the problem efficiently and effectively – and the policy will pay for their services if the claim goes through. |
3. Contain The Breach
| At this point you have identified the breach, and if you have a cyber insurance policy, contacted the nominated incident response team; now you need to contain the breach, so it doesn’t get any worse. This step is typically handled by the incident response team or your internal/external IT team.
There will be certain steps the IT team (yours or the one nominated by the emergency response team) will take to restore your system’s security and resolve the breach; this can include: |
This can be a complicated process, which is why it’s important to have access to the specialists who can handle the situation appropriately and mitigate the problem before it potentially gets too severe. |
4. Investigate The Breach & Assess The Impact
| You have contained the breach, but still don’t know what exactly happened and the extent of the damages. This is when you would typically utilise a forensic IT specialist to dig into the cause and effect of the cyber event. | Once the forensic IT has identified what occurred and the scope of the breach, you’ll be able to plan from there on how to respond to the event. |
5. Recover Data & Systems
| Once you have contained and eradicated the breach, you can begin the process to recover your IT networks, systems, and data to continue operating. Companies with a business continuity or disaster recovery plan would likely have a specific recovery plan incorporated for these types of situations. However, even if you don’t have a formal plan, your process should include the following: |
This is something your IT team should be able to assist with.
|
6. Communication & Notification
| This step relies heavily on timing – it is important to hold off on certain communication (i.e. with clients, service providers, or those affected by the breach) until you know what exactly happened and the scope of the damages. In addition, you may also have specific notification requirements that will have associated timelines – we recommend you are aware of these in advance, to avoid missing deadlines and getting hit with fines and penalties.
This depends on the impact of the cyber incident – sometimes the event doesn’t warrant communication with these parties, in which case it is usually best practice to skip this step. Alternatively, communicating with these parties can be mandatory in certain scenarios and/or vital to your business. It is important to identify which of these options apply to your business, which is where your emergency response/crisis management team can assist.
If you are going to communicate with these parties, we recommend you wait until you have enough information to pass on a complete message to help avoid miscommunications and misunderstandings. | Consider these key messages when communicating with clients and service providers:
Depending on the size of the cyber event and your business, it may be worth appointing a public relations firm to assist with the communication step.
Certain rules & regulations around mandatory notification of privacy breaches may apply to your company. We recommend you know when to notify before any breach occurs, as you could face fines & penalties if you don’t notify within a specified time period. |
7. Evaluation & Improvement
| Use the information gathered in the previous steps to improve your cyber security measures. Not only will this strengthen your defence against future cyber attacks, but it will help your case with insurers when it is time to renew your policy. | See our Top 10 Tips to Prevent A Cyber Attack here for more information on how to prevent a cyber event. |
Tips & Tricks for a Cyber Incident Response Plan
| Consider some of the below when establishing your breach response plan:
|
|

There are different types of Cyber Attacks:
| There are several types of cyber incidents that could target a business, but we’ve outlined four of the most common here:
Phishing & Social Engineering
Malware | DoS/DDoS Attack “Denial of Service Attacks” are when a website is maliciously flooded with more visitors than it’s equipped to handle, causing the website to crash.Ransomware A form of malware that holds your data captive with the threat to publish or destroy it unless their ransom is paid. |
Top 10 Tips to Prevent A Cyber Attack

1. Leverage Proactive Technology
| There are hundreds of companies out there who specialise in cyber security – use them to your advantage! | These companies offer all sorts of proactive technology for preventing cyber attacks: antivirus and antispyware software, intrusion detection systems (sometimes they happen without you even noticing), intrusion protection systems, spam filters, and multi-factor authentication software to name just a handful. |
2. Staff Training
| Technology is great, however, all the technology in the world won’t protect you from one of the most common causes of a data breach or cyber incident: human error. Therefore, it is important to continually educate your staff on cyber and data security – preferably with training programs specialised to their actual role. | This doesn’t have to be super complex “tech-y” stuff either; simple preventative measures like creating strong passwords, safeguarding private & personal information and questioning the authenticity of emails can make a huge difference. |
3. Cyber Security Audits
| As your company grows, it is important to make sure your cyber security is keeping pace. Having a Cyber Security Audit is a good way to identify any weaknesses in your security measures to minimise the risk of a cyber incident or data breach. | There are good consultants out there who specialise in identifying the holes in your system and procedures, and who will also assist in building out your security measures as your company grows. |
4. Protect Important Information to Avoid Data Breaches
| You have most likely heard about some of the massive data breaches affecting millions of consumers over the last few years. This has never been more relevant as it is today, and protecting personal & private information is something that all companies – not just multinationals – need to take seriously. | Methods for doing this can range from encrypting data when stored or sent online, refusing to collect certain information (i.e. credit cards) and implementing security measures to protect your data from hackers (see our first point above). |
5. Vulnerability & Patch Management
| How secure is your system? Vulnerability management is a proactive approach to managing network security, while patch management takes care of fixing these holes. | It is fairly straightforward to implement one of these processes: check, identify and verify any vulnerabilities, mitigate losses from these vulnerabilities, then finally apply “patches” to fix the problem. |
6. Identity Verification
| This is without a doubt the most important preventative measure for phishing and social engineering attacks. If you receive an email/call to pay an invoice or update payment information, you should always verify who the person is before actioning their request to make sure it’s not fraudulent – don’t trust the person who is contacting you without verifying they are who they say. | For example, find a contact you know in the company and call them directly to verify the request, but do not do this by responding to the email or calling a number included in the email. |
7. Third Party Vendors/Supplier Management
| You can implement all these tools to protect your information, but how do you make sure the companies you work with are doing the same? | It is important to consider how the vendors and suppliers you work with are using, storing and protecting your private and important information or data. |
8. Back-Up Your Data
| It is absolutely essential to back-up your data and information these days, but there are different ways to do this and some ways are better than others. | Arguably the best option is cloud storage, as it can include end-to-end encryption of your data to keep it safe, external back-ups, and a server dedicated to saving data. |
9. Physical Security
| Your software isn’t the only way for an attacker to access your system and wreak havoc. They can access your system using ID badges, credit cards, private files, mobile devices and computers. | Your personnel should be trained to keep these items secure at all times. |
10. Policies, Practices and Procedures
| Who doesn’t love writing policies and procedures? Although this can be a tedious exercise that many overlook, it really does encompass a lot of the above points and can be invaluable for protecting your company from a cyber event. | Most companies should implement some, if not all, of the following: Cyber Crisis Management Plan (you’ve been hacked – now what?), data breach reporting plan (reporting is almost always required/recommended), multifactor authentication for staff, password guidelines, email guidelines, among others. |
What Happens if a Cyber Attack Occurs Anyway?
| You can take every possible step in preventing a Cyber Attack and one may still occur. This is why it’s important to manage this risk by putting a Cyber Insurance policy in place. Visit our Cyber webpage for details. |